The Professional Internet Solution 662999121 Guide offers a structured approach to secure, scalable digital operations. It emphasizes governance, objective vendor evaluation, and measurable outcomes. The framework balances cost, security posture, and compliance within scalable architectures. By aligning security needs with procurement budgets and enforcing disciplined change management, it enables transparent negotiation and risk-aware decisions. The path promotes ongoing improvement and avoids vendor lock-in, leaving a clear question for practitioners as they consider next steps.
What Is Professional Internet Solution 662999121 and Why It Matters
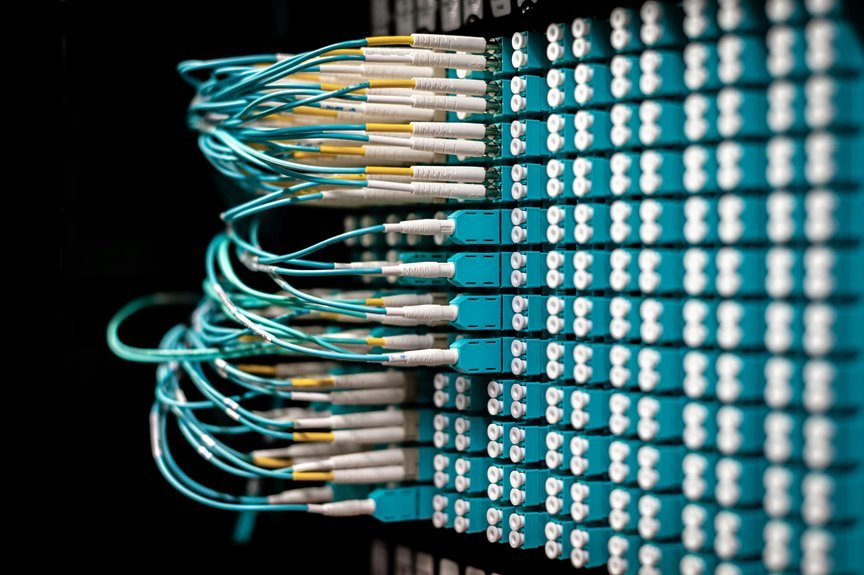
Professional Internet Solution 662999121 refers to a specific set of online services and frameworks designed to optimize digital operations, security, and performance for organizations.
The concept centers on scalable infrastructure, governance, and interoperability.
It highlights a professional internet approach where stakeholders seek measurable outcomes.
This emphasis supports informed decision-making, emphasizing thorough solution evaluation, risk awareness, and clear criteria without vendor bias or overcommitment.
How to Evaluate Providers for 662999121-Based Projects
Evaluating providers for 662999121-based projects requires a structured, criteria-driven approach that prioritizes measurable outcomes and interoperability. The process emphasizes objective vendor comparison and rigorous risk assessment, focusing on service levels, security posture, compliance, and total cost of ownership. Decisions should reflect freedom through transparent negotiation, clear benchmarks, and documented rationale, ensuring compatibility with existing architectures and future scalability.
Practical Steps to Implement Secure, Cost-Aware Solutions
To implement secure, cost-aware solutions, the process begins with aligning security requirements and cost constraints established during provider evaluation with concrete, actionable steps.
Stakeholders define secure budgeting thresholds and tie them to procurement, deployment, and governance activities.
A scalable architecture is designed to adapt resources efficiently, ensuring risk controls remain proportional while cost visibility improves through continuous monitoring and disciplined change management.
Measuring Success and Iterating for Continuous Improvement
Measuring success and guiding continuous improvement commence with establishing objective, trackable metrics that align security, cost, and governance goals.
The approach documents measuring progress, monitors performance against benchmarks, and informs refining strategies. It includes evaluating vendors, revising security budgeting, and reallocating resources as needed.
This detached framework ensures disciplined iteration, transparency, and sustained advancement toward strategic aims while preserving organizational freedom.
Conclusion
In the end, the guide leaves readers on the edge of a decision. Governance, metrics, and transparent vendor evaluation converge, shaping a path that promises security and scalability without lock-in. Yet the outcome hinges on disciplined change management and vigilant monitoring. As stakeholders weigh costs against risk, the practical steps and measurable targets become pivotal. The finish line remains near, with each incremental win sharpening clarity—until, suddenly, the optimal 662999121 solution reveals itself.